If you have ever lost a deal because a prospect asked for your ISO 27001 certificate and you did not have one, you already understand why information security matters for startups. The question "Can you share your security documentation?" has become as common in B2B sales conversations as asking about pricing or implementation timelines. Enterprise buyers, investors, and partners now expect startups to demonstrate mature security practices from day one, and an Information Security Management System sits at the heart of meeting those expectations.
This guide walks you through everything you need to know about building an ISMS that works for your startup and aligns with ISO 27001 requirements. You will learn what an ISMS actually is, why it matters specifically for growing companies, how to implement one without overwhelming your team, and what to expect on the path to certification. Whether you are exploring this topic for the first time or preparing for your certification audit, this guide gives you the practical foundation you need.
What Is an ISMS?
An Information Security Management System is a formal, documented framework that defines how your company protects sensitive information. Rather than treating security as a collection of disconnected tools and practices, an ISMS brings everything together into a coherent system with clear policies, assigned responsibilities, measurable objectives, and processes for continuous improvement.
Think of it like the difference between a house built from a blueprint versus one constructed by randomly adding rooms whenever someone felt like it. Both might technically be houses, but only one has a logical structure, proper foundations, and systems that work together efficiently. An ISMS provides that blueprint for your security program, ensuring every control, policy, and procedure serves a defined purpose and connects to your broader security objectives.
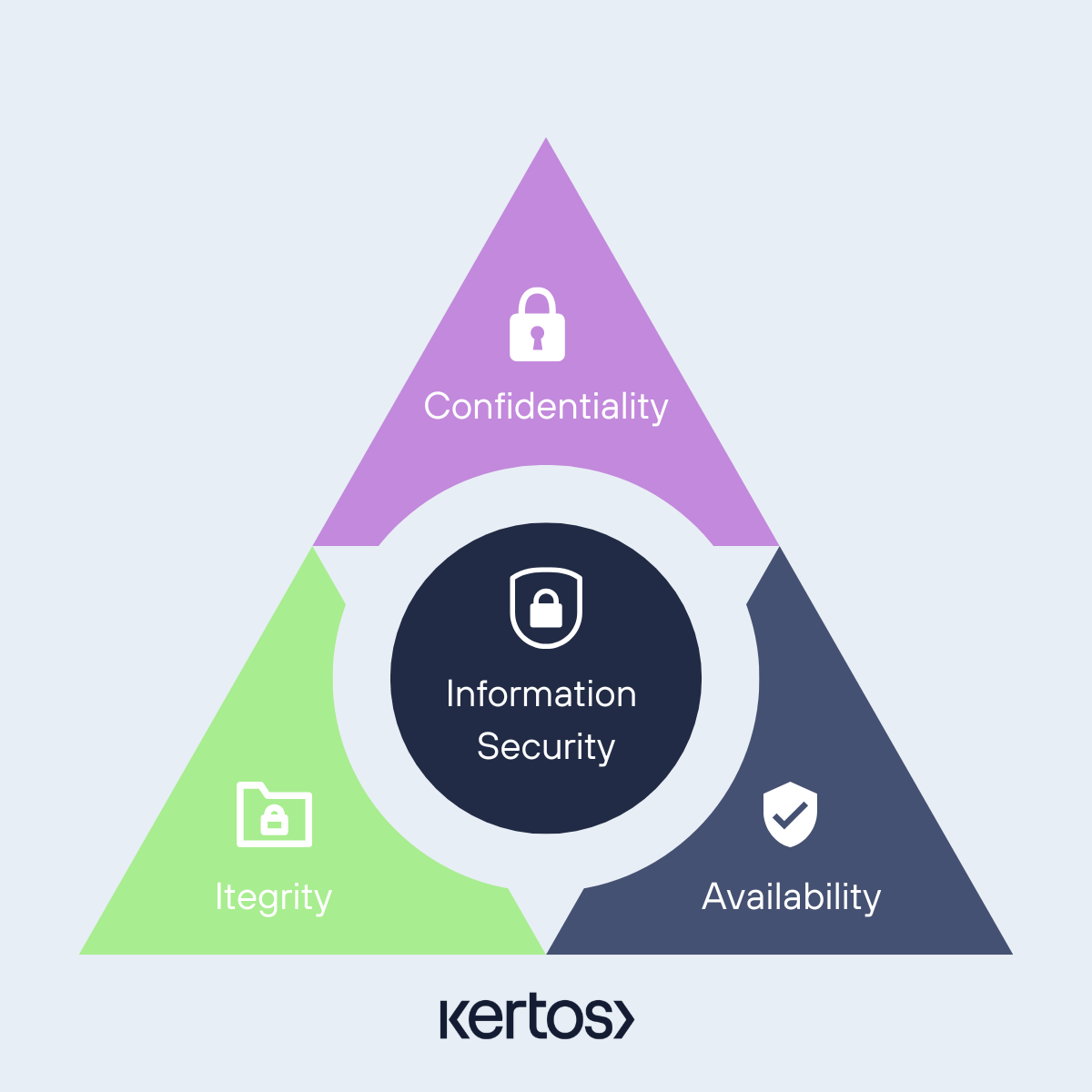
The core purpose of any ISMS is to protect three fundamental properties of information, often called the CIA triad. Confidentiality ensures that sensitive data remains accessible only to authorized people. Integrity ensures that information stays accurate and has not been tampered with. Availability ensures that authorized users can access information when they need it. Every security control in your ISMS ultimately serves one or more of these three goals.
What makes an ISMS particularly valuable is its systematic approach to risk. Instead of implementing security measures based on assumptions or reacting to incidents after they happen, an ISMS requires you to identify your specific risks, assess their likelihood and impact, and implement controls proportionate to those actual risks. This means you invest your limited resources where they matter most rather than chasing every theoretical threat.
Why Is an ISMS Critical for Startups?
Many startup founders assume that information security is a concern for large enterprises with dedicated security teams and compliance departments. This assumption has become increasingly costly as the business landscape has shifted. Today, your security posture directly affects your ability to close deals, raise funding, and build partnerships.
The reality is that startups often handle extremely sensitive information despite their size. You might be processing customer payment data, storing personal information subject to GDPR, managing intellectual property worth millions, or holding access credentials to your clients' systems. A single breach can destroy the trust you have spent years building with customers, and for a startup without the financial reserves of an established company, the consequences can be existential.
Beyond risk mitigation, an ISMS creates concrete business advantages that directly impact your growth. When you compete for enterprise contracts worth €500,000 or more, the buying company's procurement and security teams will evaluate your security practices as thoroughly as they evaluate your product. Having an ISO 27001 certified ISMS transforms security questions from deal blockers into deal differentiators. You move from "we take security seriously" to "here is our certificate, here is our Statement of Applicability, and here is how we manage these risks."
An ISMS also provides the foundation for scaling securely. Early-stage startups can sometimes manage security through informal practices and tribal knowledge, but this approach breaks down quickly as you add team members, expand your tech stack, and onboard more customers. The policies and processes you establish in your ISMS create repeatable, consistent security practices that new employees can follow immediately. You stop depending on specific people remembering to do the right thing and start relying on documented systems that work regardless of who is executing them.
Consider the practical difference this makes. Without an ISMS, onboarding a new developer might involve someone verbally explaining your access control practices, perhaps showing them how to set up their security tools, and hoping they follow the same procedures as everyone else. With an ISMS, you have documented access control policies, defined provisioning procedures, required security training modules, and records showing that each step was completed. When an auditor or customer asks how you handle access management, you have a clear, verifiable answer.
Startups often think information security is something only large enterprises need to worry about. That assumption is risky.
Here’s why an ISMS matters for startups:
- Builds customer trust from day one. When you can explain how you protect data, prospects will choose you over competitors who cannot.
- Makes scaling secure. As your business grows, so too does the volume and value of your data. An ISMS ensures security practices grow with you.
- Reduces risk dramatically. By identifying vulnerabilities early and tracking them continually, your team can reduce breaches and their financial and reputational cost.
- Supports strategic decision making. Information security becomes part of every new product, feature, or partnership discussion.
Think of your startup as a ship. Without navigation tools (an ISMS), every storm risks capsizing you. With a system in place, you steer toward opportunity and away from hazards, making security part of your strategic journey.
What Are the Core Components of an Effective ISMS?
Building an ISMS that actually works requires several interconnected components. Understanding these elements helps you approach implementation systematically rather than treating each requirement as an isolated checkbox.
Information Security Policies
Your policies form the foundation of your ISMS, establishing the rules and principles that govern how your company handles security. These are not generic templates downloaded from the internet but documents that reflect your actual business context, risk appetite, and operational reality.
A startup's policy framework typically includes an overarching information security policy that sets the tone and direction, supported by specific policies covering areas like acceptable use, access control, data classification, incident response, and vendor management. The key is making these policies practical and actionable rather than aspirational documents that no one reads. If your acceptable use policy prohibits something your team does every day, the policy is meaningless. Effective policies describe what people actually should do, in language they can understand, with clear consequences for non-compliance.
Risk Assessment and Treatment
Risk assessment is where your ISMS becomes tailored to your specific situation. You identify the assets that matter most to your business, the threats that could affect them, the vulnerabilities that could be exploited, and the potential impact if something goes wrong. This analysis drives every other decision in your ISMS.
The ISO 27001 standard requires a formal risk assessment methodology but does not prescribe exactly how you must conduct it. For startups, a practical approach involves creating an asset inventory that documents your critical information and systems, identifying realistic threat scenarios based on your industry and technology stack, scoring risks based on likelihood and impact, and then deciding how to treat each risk. Your treatment options include implementing controls to reduce the risk, transferring it through insurance or contractual arrangements, avoiding it by changing your practices, or accepting it if the risk falls within your defined tolerance.
Security Controls
Controls are the actual mechanisms that reduce your risks. These include technical controls like encryption, firewalls, and multi-factor authentication. They include physical controls like office access restrictions and device security. And critically, they include administrative controls like policies, training, and defined procedures.
ISO 27001 provides Annex A, which contains 93 controls organised into four categories: organisational controls, people controls, physical controls, and technological controls. You do not need to implement every control, but you must consider each one and document why you have included or excluded it in your Statement of Applicability. This document becomes a key artifact in your certification audit, demonstrating that your control selection is justified by your risk assessment rather than arbitrary.
Incident Management
Even the best security programs experience incidents. What separates mature companies from vulnerable ones is how they respond. Your ISMS should define clear procedures for detecting security events, assessing whether they constitute actual incidents, containing damage, eradicating the threat, recovering normal operations, and learning from what happened.
For startups, incident management does not require a 24/7 security operations center. It requires documented procedures, defined roles, tested communication channels, and a commitment to learning from every incident. When your first significant incident occurs, having a written playbook makes the difference between a coordinated response and panicked improvisation.
Continuous Improvement
An ISMS is not a project you complete and then forget. The threat landscape evolves constantly, your business changes, new vulnerabilities emerge, and attackers develop new techniques. Your ISMS must include mechanisms for monitoring effectiveness, identifying weaknesses, and driving improvement.
This typically involves regular internal audits that test whether controls are working as intended, management reviews that assess the overall health of your security program, and corrective action processes that address identified problems. ISO 27001 specifically requires this continuous improvement cycle, ensuring your ISMS becomes more effective over time rather than stagnating.
What Is the Relationship Between ISMS and ISO 27001?
Understanding how ISMS and ISO 27001 relate to each other helps you approach certification with clarity. The ISMS is the system you build and operate. ISO 27001 is the international standard that defines what a credible ISMS should look like and how to demonstrate that yours meets recognized requirements.
ISO 27001 was developed by the International Organization for Standardization and the International Electrotechnical Commission. The current version, published in 2022, updated the previous 2013 version with modernized controls reflecting current technology practices and threat landscapes. The standard specifies requirements for establishing, implementing, maintaining, and continually improving an ISMS within the context of your business risks.
When you pursue ISO 27001 certification, an accredited external auditor examines your ISMS to verify it meets the standard's requirements. This audit happens in two stages. Stage 1 reviews your documentation to confirm your ISMS is ready for a full audit. Stage 2 involves the auditor visiting your operations, interviewing staff, examining evidence, and testing whether your controls work as documented. If you pass both stages, you receive your certificate, valid for three years with annual surveillance audits confirming you maintain compliance.
The certification provides objective proof that your security practices meet internationally recognized standards. For European startups especially, ISO 27001 has become the de facto requirement for doing business with enterprises. While American companies might accept SOC 2 attestations, European buyers overwhelmingly prefer ISO 27001 because it aligns with the risk management frameworks they use internally and complements regulatory requirements like GDPR.
Importantly, around 70% of ISO 27001 requirements overlap with other compliance frameworks including SOC 2, NIS2, DORA, and TISAX. Building your ISMS properly creates a foundation that makes achieving additional certifications dramatically easier. You are not starting from scratch each time but extending and adapting work you have already completed.
How Do You Implement an ISMS for ISO 27001 Certification?
Implementing an ISMS might seem overwhelming when you look at the full scope of ISO 27001, but breaking it into manageable phases makes the process achievable even for small teams. The following roadmap reflects what has worked for thousands of European companies achieving certification.
Phase 1: Define Your Scope and Context
Before you can build an effective ISMS, you need to understand what you are protecting and why. Start by defining the scope of your ISMS, which means identifying which parts of your business, which information assets, and which systems will be covered. A focused scope is not a weakness. In fact, it often makes certification faster and more practical.
For most startups, the scope covers your primary product or service and the supporting infrastructure. If you are a SaaS company, your scope likely includes your production environment, customer data processing, development practices, and corporate systems. You do not necessarily need to include every aspect of your business if certain areas do not handle sensitive information or face significant security risks.
You also need to understand your context, meaning the internal and external factors that affect your security program. This includes regulatory requirements you must meet, contractual obligations from customer agreements, industry expectations, your technology stack, your team's capabilities, and your business objectives. This context shapes everything that follows.
Phase 2: Secure Leadership Commitment and Establish Governance
ISO 27001 explicitly requires top management commitment. This is not just a formality. Without genuine leadership support, your ISMS will lack the resources, authority, and organizational priority needed to succeed.
In practical terms, leadership commitment means your founders or executives formally approve the information security policy, allocate budget and time for implementation, assign clear accountability for the ISMS, and participate in management reviews. For startups where the CEO is also handling sales, product, and fundraising, this might feel like another demand on a limited bandwidth. However, the alternative is an ISMS that exists on paper but does not actually protect your business.
Establish your governance structure by defining who is responsible for information security. Many startups designate a Chief Information Security Officer or equivalent role, even if that person also holds other responsibilities. Define reporting lines, decision-making authorities, and how security gets integrated into business decisions.
Phase 3: Conduct Your Risk Assessment
With your scope defined and governance established, you can conduct a meaningful risk assessment. This process identifies what could go wrong, evaluates how likely and impactful each scenario is, and prioritizes where you need to focus your security efforts.
Start by inventorying your information assets. This includes customer data, source code, financial records, employee information, intellectual property, and the systems that process and store this information. For each significant asset, identify realistic threats based on your specific context. A startup handling payment data faces different threats than one processing health records or industrial control data.
Assess each identified risk based on two factors: how likely is this scenario to occur, and what would be the impact if it did? You can use qualitative scales like low, medium, and high, or quantitative approaches if you have sufficient data. The goal is consistent, defensible risk scoring that supports rational decision-making.
Document your findings in a risk register that becomes a living document throughout your ISMS lifecycle. For each risk, record the asset affected, the threat scenario, your likelihood and impact assessment, the overall risk level, and your treatment decision.
Phase 4: Select and Implement Controls
Your risk assessment tells you where you need protection. Now you select controls that address those risks appropriately. ISO 27001 Annex A provides a comprehensive control catalog, but your selection should be driven by your specific risks rather than a blanket attempt to implement everything.
For each control in Annex A, document whether you have implemented it and justify your decision. If you exclude a control, explain why it does not apply to your context. This justification goes into your Statement of Applicability, a required document for certification that shows auditors your control selection is rational and risk-based.
Implementation means more than writing policies. It means actually putting controls into operation, configuring systems appropriately, training people on new procedures, and verifying the controls work as intended. A written access control policy means nothing if your actual systems allow unrestricted access.
Prioritize controls that address your highest risks first. You do not need perfect implementation everywhere to achieve certification. You need appropriate controls in place, functioning as documented, with evidence you can demonstrate to an auditor.
Phase 5: Build Documentation and Collect Evidence
Documentation serves two purposes in your ISMS. Internally, it ensures consistency and supports training. Externally, it demonstrates to auditors that your controls exist and function properly.
Required documentation for ISO 27001 includes your information security policy, your risk assessment methodology and results, your Statement of Applicability, your risk treatment plan, and evidence that your controls operate effectively. Beyond these requirements, document procedures for critical processes like incident response, access provisioning, change management, and backup recovery.
Evidence collection becomes much easier when you integrate it into daily operations rather than treating it as an audit preparation activity. Modern compliance platforms can automatically collect evidence from your systems, pulling access logs, configuration snapshots, completed training records, and other artifacts that demonstrate control effectiveness. This continuous evidence collection reduces the scramble before audits and gives you ongoing visibility into your security posture.
Phase 6: Train Your Team
Security controls are only as effective as the people implementing them. Your ISMS needs a training and awareness program that ensures everyone understands their security responsibilities and follows established procedures.
For startups, training does not require elaborate programs. It requires relevant, practical content that connects to people's actual work. Developers need to understand secure coding practices and change management procedures. Customer support staff need to recognize social engineering attempts and follow data handling policies. Everyone needs to understand your acceptable use policy, incident reporting procedures, and their role in protecting company information.
Document training completion and assess understanding through quizzes or practical exercises. This evidence demonstrates to auditors that your team is capable of executing your security controls properly.
Phase 7: Monitor, Audit, and Improve
Before your certification audit, conduct internal audits that test whether your ISMS operates as documented. These audits identify gaps you can address before an external auditor finds them.
Internal audits should cover each area of your ISMS over time, testing whether policies are followed, controls function properly, and documentation stays current. When you find problems, document them as nonconformities and track corrective actions to resolution.
Management reviews bring leadership into the ISMS cycle, examining audit results, incident trends, resource needs, and improvement opportunities. These reviews demonstrate that your ISMS receives appropriate executive attention and adapts to changing circumstances.
What Common Challenges Do Startups Face When Building an ISMS?
Understanding typical obstacles helps you prepare for them and maintain momentum through implementation.
Limited Resources and Competing Priorities
Startup teams are stretched thin, and adding ISMS implementation to everyone's workload can create friction. The solution is not to delay security until you have more resources but to approach implementation pragmatically. Focus on controls that address your highest risks first. Use templates and tools that reduce documentation burden. Accept that your initial ISMS will not be perfect and plan for iterative improvement.
Automation makes a significant difference here. Platforms that integrate with your existing tech stack can automatically collect evidence, track control status, and identify gaps, reducing the manual effort required from your team by 80% compared to spreadsheet-based approaches. This is especially valuable for small teams where everyone has multiple responsibilities.
Making Security Part of the Culture
People resist security controls when they perceive them as bureaucratic obstacles that slow down their real work. Overcoming this resistance requires connecting security to business objectives everyone cares about. When your sales team understands that ISO 27001 certification enables enterprise deals, when developers see that secure coding practices prevent the 3am production incidents they hate, security transforms from an imposed requirement to a shared value.
Lead by example. If founders and executives follow security policies visibly and consistently, the rest of the organization follows. If leadership treats security as optional or routinely bypasses controls for convenience, no amount of policy documentation will create a secure culture.
Keeping Pace with Change
Your ISMS cannot be static because your business is not static. New products, new integrations, new team members, and new threats all affect your risk landscape. Build review cycles into your normal operations. When you add a significant new system or integration, assess its security implications. When you onboard a new vendor, evaluate them against your vendor management criteria. When you experience an incident, update your controls and procedures based on lessons learned.
This continuous improvement approach means your ISMS becomes stronger over time rather than degrading as your business evolves.
What Benefits Does a Mature ISMS Deliver?
A well-implemented ISMS transforms compliance from a burden into a business advantage in several concrete ways.
The most immediate benefit for many startups is closing deals that would otherwise be impossible. Enterprise buyers increasingly require ISO 27001 certification as a procurement prerequisite. Having your certificate ready means security reviews become brief validation exercises rather than extended negotiations. You spend less time responding to questionnaires and more time discussing how your product solves customer problems.
Regulatory compliance becomes dramatically simpler when you have an ISMS foundation. GDPR requires risk-based security measures, accountability, and documented processes, all things your ISMS provides. If you later need DORA compliance for financial sector clients or NIS2 compliance as regulations expand, the 70% overlap with ISO 27001 means you have already done most of the work.
Operationally, an ISMS creates predictability. Incidents still happen, but your response is coordinated rather than chaotic. Audits become routine reviews rather than emergency preparation scrambles. New employees understand their security responsibilities from day one. You spend less time reinventing processes and more time improving them.
Perhaps most importantly, you build the foundation for secure growth. The ISMS you create today scales with your business. The policies you write, the controls you implement, and the culture you establish become more valuable as you handle more customers, more data, and higher stakes.
A well-implemented ISMS can deliver:
- Reduced likelihood of breaches and outages.
- Improved customer assurance and competitive advantage.
- Easier compliance with regulations like GDPR, SOC2, and more.
- A strategic framework that supports growth with confidence.
Many startups find that an ISMS becomes the backbone of how they handle security and privacy, creating predictable, audit-ready processes that save time and cost.
Moving Forward with Your ISMS
Building an ISMS and achieving ISO 27001 certification represents one of the most valuable investments a growing startup can make. You gain the ability to compete for enterprise contracts, demonstrate mature security practices to customers and investors, reduce your actual security risks, and establish foundations that scale with your business.
The path from today to certification is clearer than it might appear. Define your scope, assess your risks, implement appropriate controls, document what you do, and prove your system works. With the right approach and appropriate tools, you can complete this journey in weeks rather than months.
If you are ready to transform compliance from a burden into a competitive advantage, start by understanding where you stand today. A gap assessment shows you exactly what you need to address for certification and creates a clear roadmap for getting there. Take the first step and see how straightforward the path to ISO 27001 certification can be.

Frequently Asked Questions (FAQs) About ISMS for Startups
What exactly is an ISMS in simple terms?
An ISMS is the complete system your company uses to manage information security. It includes your security policies, the processes you follow, the controls you implement, the people responsible for security, and the mechanisms for monitoring and improving over time. Think of it as the organized approach to protecting your most valuable information rather than addressing security problems randomly as they arise.
Why should a startup invest in an ISMS before becoming a large company?
Waiting until you are large makes implementation harder, not easier. Small teams can establish security foundations more quickly because there is less complexity to manage, fewer legacy systems to accommodate, and stronger alignment between team members. More practically, your customers and prospects are asking about your security practices now. Enterprise deals worth €100K or more regularly depend on having ISO 27001 certification. The startup that gets certified in six weeks wins the deal while competitors spend months explaining why they are working on it.
How is ISO 27001 different from having an ISMS?
The ISMS is your actual security management system. ISO 27001 is the international standard that defines what a good ISMS should include and how to prove yours meets those requirements. You can have an ISMS without ISO 27001 certification, but without the certification, you cannot demonstrate to customers that an independent third party has verified your security practices meet recognized international standards.
Can a startup with 15 people actually achieve ISO 27001 certification?
Absolutely. ISO 27001 is designed to scale to any organization size. What changes is the complexity of implementation, not the feasibility. A 15-person startup typically has a simpler technology environment, fewer processes, and less bureaucracy than a 500-person company. This means a tighter scope, faster implementation, and a more straightforward audit. With proper guidance and appropriate tooling, many startups achieve certification in six to eight weeks.
How long does ISMS implementation typically take for a startup?
Implementation timelines vary based on your starting point, your scope, and the resources you allocate. A focused startup that prioritizes implementation can often establish a functional ISMS and achieve certification within six to twelve weeks. The traditional approach using external consultants often takes six to twelve months, but modern compliance platforms with automation and expert guidance compress this timeline dramatically while requiring only 15 to 20 hours of your team's time.
Is an ISMS only about technical security controls?
Technical controls like encryption, access management, and network security are important components, but an ISMS addresses people and processes equally. Some of your most significant risks come from human factors: employees who fall for phishing attacks, vendors with poor security practices, or processes that create opportunities for error. Your ISMS includes security awareness training, vendor management procedures, access control policies, and incident response plans alongside the technical mechanisms.
What happens if we fail the certification audit?
Certification audits rarely result in outright failure if you have prepared appropriately. More commonly, auditors identify specific nonconformities that you need to address before receiving your certificate. You receive a report detailing the issues, implement corrective actions, and the auditor verifies those corrections. Treating audit findings as improvement opportunities rather than failures keeps the process constructive. With proper preparation including internal audits and gap assessments, significant surprises at certification time are rare.
How much does ISMS implementation and ISO 27001 certification cost?
Traditional approaches using external consultants often reach six-digit costs when you account for consulting fees, internal time, and audit costs. Modern compliance platforms with automation and integrated expert support reduce this dramatically, typically to under €15,000 all-in for startups with straightforward scopes. The certification audit itself typically costs between €5,000 EUR and €15,000 depending on your scope and the certifying body.
Does ISO 27001 certification help with other compliance requirements?
Significantly. Approximately 70% of ISO 27001 requirements overlap with other frameworks including SOC 2, GDPR, NIS2, DORA, and TISAX. Once you have your ISO 27001 ISMS in place, adding compliance with additional frameworks requires extending your existing system rather than starting from scratch. For European companies that need multiple certifications for different customer segments, this framework overlap creates substantial efficiency gains.
What Are the Core Components of an Effective ISMS?
An effective ISMS should include:
- Information Security Policies. Clear, written definitions of how security is handled in your organization.
- Risk Assessment and Treatment. Systematic identification of threats, evaluation of their impact, and controls to reduce unacceptable risks.
- Security Controls. The practical mechanisms, policies, and procedures that enforce protection. These should align with recognized frameworks.
- Incident Management. Defined steps for detecting, reporting, and responding to security breaches.
- Performance Monitoring and Improvement. Regular reviews, audits, and improvement plans that ensure your ISMS evolves with your risk landscape.
How Does an ISMS Work in Practice?
At its heart, an ISMS is a cycle:
- Understand your context. Know what information you need to protect and why.
- Assess risks. What could go wrong? How likely is it? What will the impact be?
- Treat risks. Decide what security measures reduce your biggest threats.
- Monitor and measure. Track whether your controls work over time.
- Improve continually. Attackers change their tactics, and so must you.
This cycle forms a continuous feedback loop rather than a one-time project.
What’s the Relationship Between ISMS and ISO27001?
ISO27001 is the international standard that defines how to build, implement, maintain, and continually improve an ISMS. In essence:
- An ISMS is the system you build and operate.
- ISO27001 is the framework that tells you how to do that well and how to prove compliance.
Achieving ISO27001 certification means a third party has audited your ISMS and confirmed it meets globally-recognized information security requirements.
You can think of ISO27001 as the architectural blueprint for the fortress: it tells you what walls, gates, and watchtowers you need, and how to verify they are effective.
How Do You Implement an ISMS With ISO27001?
While implementation can be adapted to your size and needs, there’s a reliable roadmap:
- Define the scope of your ISMS. What business units, information types, and systems are included?
- Set leadership support and policy. Leadership must commit to resources and authority for the ISMS.
- Perform risk assessment and planning. Identify threats, impacts, and appropriate controls.
- Select and implement controls. Apply policies and technologies to manage risk.
- Train your team. Awareness and understanding across your startup reduces human error.
- Monitor, audit, and improve. Collect metrics and react to changes in your risk environment.
This implementation becomes smoother when you choose tools and templates that align with ISO27001 requirements, making audit preparation significantly easier.

.svg)












